Device Registry Overview Covering dk380c4.0-h8 Model Size and Monitoring Logs

The device registry for dk380c4.0-h8 focuses on a compact yet capable model size and predictable resource usage. It standardizes metrics such as checkpoint bytes, model.graph size, and serialization footprints to enable consistent comparisons across deployments. Monitoring logs are integrated to track performance over time, supporting traceability, governance, and anomaly detection. This combination informs lifecycle planning and deployment optimization, inviting consideration of how these measures will influence future decisions and configurations.
What Is the dk380c4.0-h8 and Why Its Model Size Matters?
The dk380c4.0-h8 is a model variant whose architectural design and parameter configuration define its performance and deployment characteristics.
The dk380c4.0 h8 overview emphasizes compact yet capable structure, while the model size significance relates to deployment flexibility, resource use, and scalability.
It provides predictable behavior, facilitating freedom in integration, monitoring, and lifecycle planning across diverse environments.
How to Measure and Compare Model Size Across Deploys?
In practice, measuring model size across deploys requires consistent definitions and tooling to ensure comparability. Size tracking implements a stable metric—bytes in checkpoint, model.graph size, and serialization footprint—across environments. Deploy comparison relies on versioned artifacts and standardized reporting. This approach minimizes ambiguity, supports auditability, and clarifies drift implications for resource planning and capacity decisions.
Monitoring Logs: Key Metrics to Track Performance Over Time
Monitoring logs provide a longitudinal view of model behavior, building on the prior discussion of size and artifact tracking by capturing runtime performance indicators and operational health over time.
The section identifies monitoring logs as essential for tracking performance trends, correlating them with model size, and enabling deployment comparisons while maintaining focus on stability, efficiency, and traceability across evolving systems.
Best Practices for Log Collection, Analysis, and Security
Effective log collection, analysis, and security for the dk380c4.0-h8 model require a structured approach that standardizes data formats, sampling rates, and retention policies across deployment environments.
The guidance emphasizes log governance, clear data ownership, and transparent performance trends while establishing robust anomaly handling to detect irregularities promptly, ensuring compliance, auditability, and resilient, freedom-friendly security postures.
Conclusion
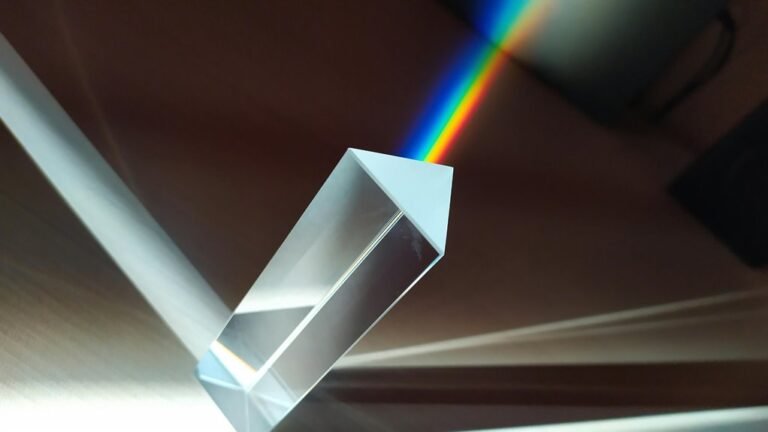
The dk380c4.0-h8 model demonstrates that compact size can coexist with robust capability, enabling predictable resource consumption and flexible deployment. By standardizing metrics such as checkpoint bytes, model.graph size, and serialization footprints, organizations can objectively compare deployments and ensure consistent governance. Monitoring logs add traceability, performance trends, and anomaly detection, essential for lifecycle optimization. Like a well-tuned instrument, precise measurements keep deployment orchestration harmonious and performance-ready across environments.