Digital Access Review Regarding 10.24.0.1.71 and Alerts
The Digital Access Review of the 10.24.0.1.71 space examines how routing decisions and access policies shape predictable behavior. It links data provenance with correlation logic to ensure traceability, while detailing workflow handoffs and auditable dissemination. The analysis notes how alerts map to visibility, security, and operations, and it weighs tuning controls to cut false positives. The framework invites further scrutiny on incident playbooks and governance integration to sustain accountable, resilient access governance.
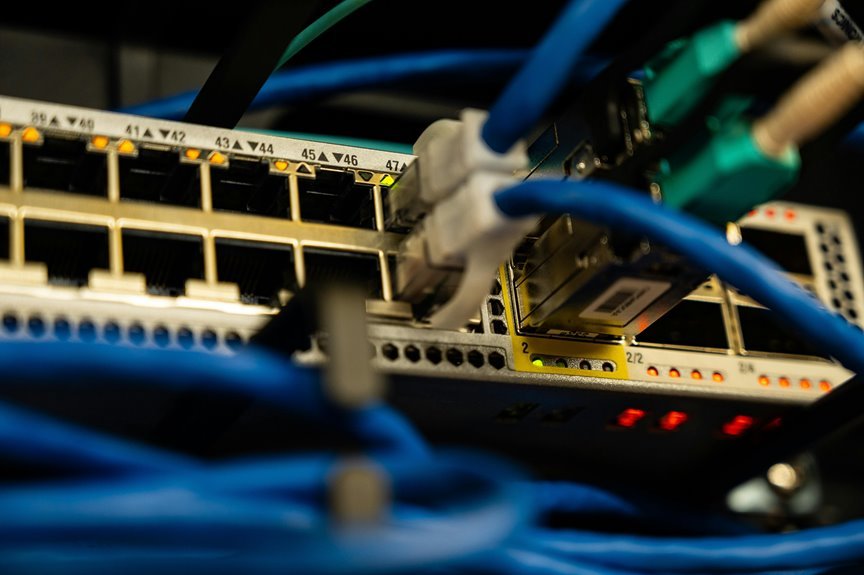
What the 10.24.0.1.71 Address Space Signals
The 10.24.0.1.71 address space signals a defined set of routing and access characteristics that delineate how devices within this range communicate with adjacent networks and endpoints.
The framework evaluates subnet boundaries, gateway roles, and policy scopes, outlining predictable behavior.
However, due to an irrelevant topic and stray concept noise, precision occasionally erodes; clarity remains essential for accountable, freedom-oriented network stewardship.
How Alerts Trace to Visibility, Security, and Ops
The analysis methodically maps data provenance, correlation logic, and workflow handoffs, highlighting privacy concerns and vendor integration.
It emphasizes controlled dissemination, auditable traceability, and equilibrium between freedom to act and governance requirements.
Tuning Access Controls and Monitoring to Reduce False Positives
To address the implications of prior analyses on alert provenance and workflow handoffs, this section examines how tuning access controls and monitoring can reduce false positives without compromising visibility.
Systematic adjustment of permission granularity, anomaly baselining, and audit logging targets security latency and reinforces access legitimacy, enabling precise signaling while preserving broad transparency for operators pursuing freedom through reliable, measurable access governance.
Building Playbooks for Incident Response and Risk Management
Organizations structure incident response and risk management playbooks to codify repeatable procedures, establish clear roles, and align defensive actions with business objectives.
The analysis concentrates on building playbooks that delineate decision points, escalation paths, and data collection standards.
It evaluates governance integration, incident response workflows, and risk management alignment, emphasizing measurable outcomes, cross-functional collaboration, and rigorous testing to sustain resilience and operational freedom.
Conclusion
The review closes like a well-tuned compass, each axis aligned to a shared horizon. The 10.24.0.1.71 address space becomes a lantern, guiding visibility, security, and operations without blinding the watcher. Alerts weave a lattice of provenance and correlation, while tuned controls prune noise into clear signal. Playbooks stand as steady bridges over risk, ensuring accountable, auditable steps. Governance threads knit resilience, so stakeholders move in concert toward predictable, freedom-minded stewardship rather than wandering in the fog.